Protect Yourself from a Ransomware Attack in Four Easy Steps

Hackers finally became businessmen. Actually, they became more like mobsters, so let’s rephrase that: hackers finally realized that they could use their “special skills” and “special powers of persuasion” to make money. And they’re doing it in droves.
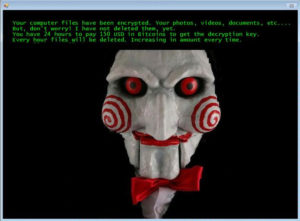
Their favorite tactic is now ransomware – they silently enter your computer and take all of your files hostage: digital photos of your wedding, wills, contracts, diaries, music, the video of your little girl’s first steps … all of it. Then they leave a ransom note in the middle of your screen:
Transfer $500 (or $1,000, or $10,000 …) to them immediately, and they’ll give you the password to get your files back. Otherwise, your files are gone.
Fighting Ransomware: Don’t Pay the Ransom!
Ransomware is spreading like wildfire for one reason: it works. Now that we’ve shifted our lives to the digital realm, precious memories that used to live on paper and prints and film now exist as a fragile sequence of 1s and 0s, as ephemeral as a stream of electrical current, and effortless to alter.
Bring on a hacker who knows how to encrypt data, and every important file you own could get locked down right under your nose. The hacker doesn’t even need to remove them from your machine. Without the “encryption key” your files will end up completely inaccessible.
In fact, it doesn’t even take a savvy hacker. The code necessary to pull off this heist floats freely around the Internet. Any 12 year-old with the slightest bit of tech savvy (i.e. all of them) can start exploiting innocent people for money without even knowing what they’re doing. And when no skills + no effort = big money, it’s easy to see why the ransomware trend is spiking quickly.
Now that you see the ugly realities, hopefully you’re asking the pertinent question: How can I protect myself against a ransomware attack? Answer: it’s pretty easy, actually. And it has nothing to do with Google Drive (or OneDrive or DropBox). And we’ll explain how in just a second.
But first, as a society, our only hope to eliminate ransomware attacks altogether is to refuse to make the payout. If there’s no profit in the game, the incentive disappears. But in order to refuse to make the payout, you must be prepared. So let’s learn how …
Ransomware Preparedness Step 1: Don’t Let it on Your Machine
The days of brute-force attacks against computers are waning. It requires too much knowledge for most would-be hackers and too much effort. So how do they get in these days? Easy: they knock. Why assault the castle walls when users are happy to open the front gate?
How does this happen? Through email. They send out a legitimate-looking email message with a link. When you click that link, it downloads their virus onto your machine. And from there, they have total control. One of their first acts will be sending out an email from your account to all of your contacts asking them to click a link. It looks legitimate because it’s from you, so they click away. And thus the virus spreads.
So your first defense against ransomware is to never click a link in an email unless you are positive it’s legitimate. There are a few things about email we’d do well to keep in mind:
- That hot little gal in the email flashing lots of skin doesn’t actually want to meet up. She’s a greasy, 16 year-old hacker.
- Facebook videos don’t come over email. They show up on Facebook.
- FedEx never emails you if they can’t deliver a package. They’ll leave a note on your door or call. Just ask yourself, “How would they have my email address?”
- The IRS isn’t going to notify you about audits or refunds through email. They use certified mail so they can have proof of delivery.
- You don’t have a long-lost, dead uncle with millions of dollars, and no attorney will ever reach out through email. Again, ask yourself: “How would they have my email address?” and “Is this sort of business typically handled through email?”
- NOTHING official comes through email. Really.
- If in doubt, email the person back and ask, “Did you send this?”
Finally, even if a link looks legitimate, ALWAYS perform this check: Hover your mouse over the link without clicking; the actual address will display at the bottom of your email. If this address doesn’t match the address in the message or if it looks suspicious, DO NOT CLICK.
Ransomware Preparedness Step 2: Don’t Rely on Your Cloud Drive to Save You
We love Google Drive, OneDrive, and DropBox. They have taken us to Nirvana … or at least, file-access Nirvana. They put our files at our fingertips wherever we wander, they make file sharing a snap, and – as an added bonus – they give us a safety net against crashed drives. But we can’t get lulled into thinking they are a true backup. In fact, ransomware exposes their weakness.
These cloud drives instantly synchronize every file change to the cloud. That being true, think through this scenario: a hacker accesses your computer and begins encrypting your files. Encryption is a change to the file. So what will your cloud drive do? Exactly. It will upload the encrypted file to the cloud. In fact, by the time you realize your computer has been compromised, every copy of your files, across every device, is now hostage.
Now, this is one area where Google, Microsoft, DropBox, and the other big players could step up and perform a public service. They could easily detect that hundreds of file changes are rolling in and that the files have been encrypted. They could then suspend the account pending your approval, thus preserving your originals. Or alternatively, they could provide a way to roll back your account a few days or weeks. But to date, none of them have owned up to the call to take a lead against ransomware.
So don’t expect your cloud drive to save your hide.
Ransomware Preparedness Step 3: Use a Real Offsite Backup Service
Offsite backup is different. Most offsite backup providers like CrashPlan, Mozy, Carbonite, and SOS keep a history of your backups. If you can determine the date when your machine got infected, you can wipe your hard drive then re-download the last clean version of your files.
It’s a simple solution that an astonishing number of businesses and home users still won’t do. It’s the ultimate case of penny-wise, dollar-stupid. Users won’t pay the equivalent of one lunch a month to protect their files, then they get strong-armed into paying $500+ to free their files from a hostage-taker. You have to assume you’ll be paying for one service or the other – protecting your files or freeing your files. Why not give your money to the legitimate business?
Ransomware Preparedness Step 4: Keep a Separate Backup
We are strong proponents of multiple backups. Given the delicate nature of digital content, you would be well-served to keep at least two current copies.
What kind of backup? Nothing elaborate. Get a large thumb drive or USB drive and make a habit of copying everything to it once a week. Burn some CDs or DVDs. Some of your data, like old bank records and financial records, will never change. So burn those items to a DVD then put them in a safe deposit box. In fact, wise users will segregate their data into two categories: Current and Archive. The Archive only needs to be backed up when you occasionally add to it. The Current data can be backed up weekly.
But here’s the important point: If you back up to an external drive, disconnect it as soon as you’re done with the backup. If you leave the drive connected, it will get taken hostage too!
Conclusion
Ransomware should give you a bit of a panic. Many users have lost their data permanently, even after paying the ransom. But with a little bit of caution and some planning on your part, you can keep a clean copy of your data safely out of their reach. Your memories and valuable documents are worth the little bit of effort.